Hosted by: Board of Directors
Did you know that The SPE- GCS gives over $100,000 annually in scholarships? On May 23rd, 2019, the annual SPE-GCS Awards Banquet recognizes the high school seniors and college students who have received SPE-GCS, Communities in Schools – Houston, or SPE Auxiliary scholarships for the 2017-18 academic year. This is a fantastic opportunity to welcome outstanding students into the petroleum industry and to make a positive impression on members of the community.

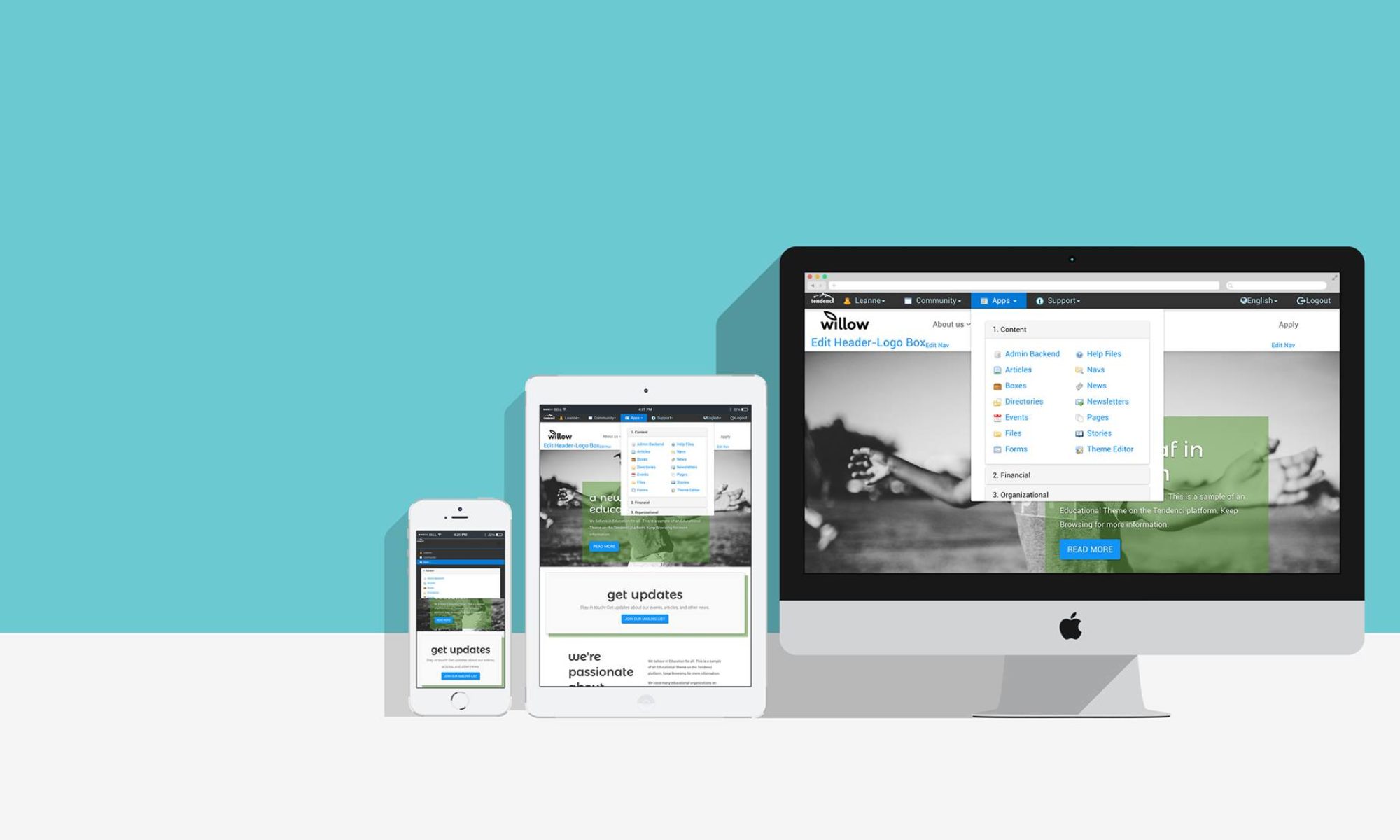
Tendenci is proud to have partnered with SPE-GCS for the last 20 years and support their mission to remain at the forefront of technology, leading the way for other organizations in the industry.
Check out the event details here.